
Yan Cui
I help clients go faster for less using serverless technologies.
A use case happened at work recently, where we need to subscribe a SQS queue to a SNS topic running in another AWS account. On the surface this seems like something many people would need to do, and indeed I was able to find an official tutorial pretty quickly. But the tutorial is all “click this in the SQS console, and do that in the SNS console”. We are strong believers in Infrastructure as Code and having someone do the subscription steps manually is not going to work, especially given that we’ll be repeating this process in many places.
So here’s what I learnt as I translate the tutorial steps into CloudFormation, and some gotchas I found.
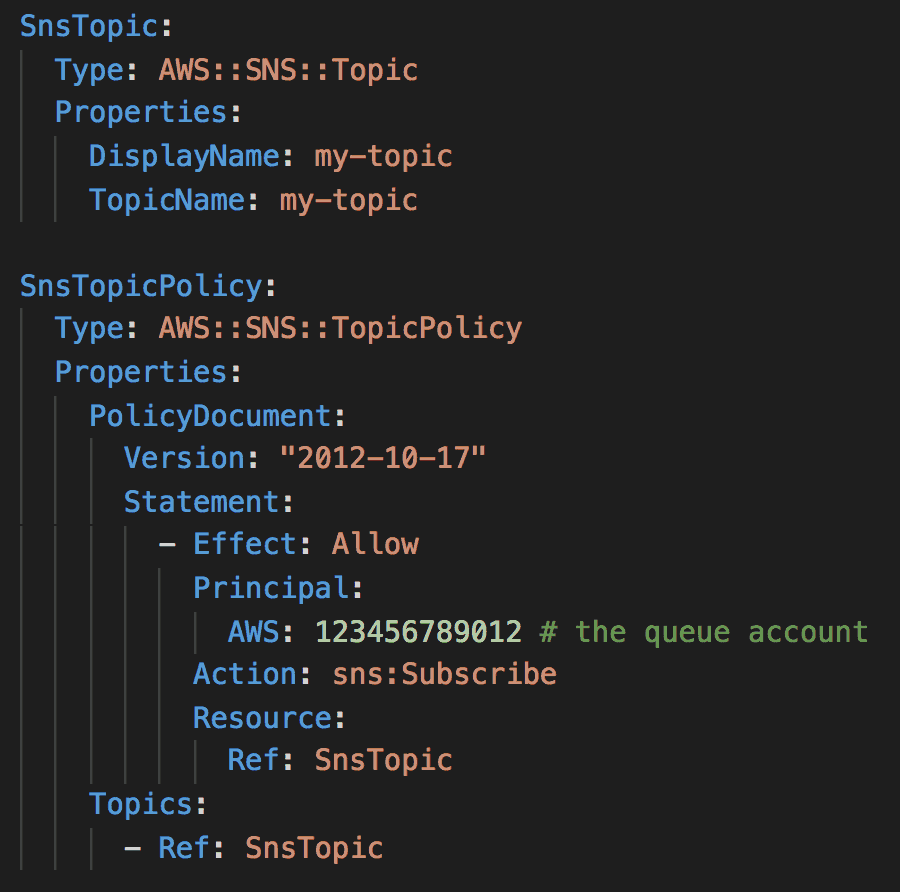
First, in the SNS account, you need to add a SNS TopicPolicy to give the SQS account permission to call sns:Subscribe on the relevant topic(s).
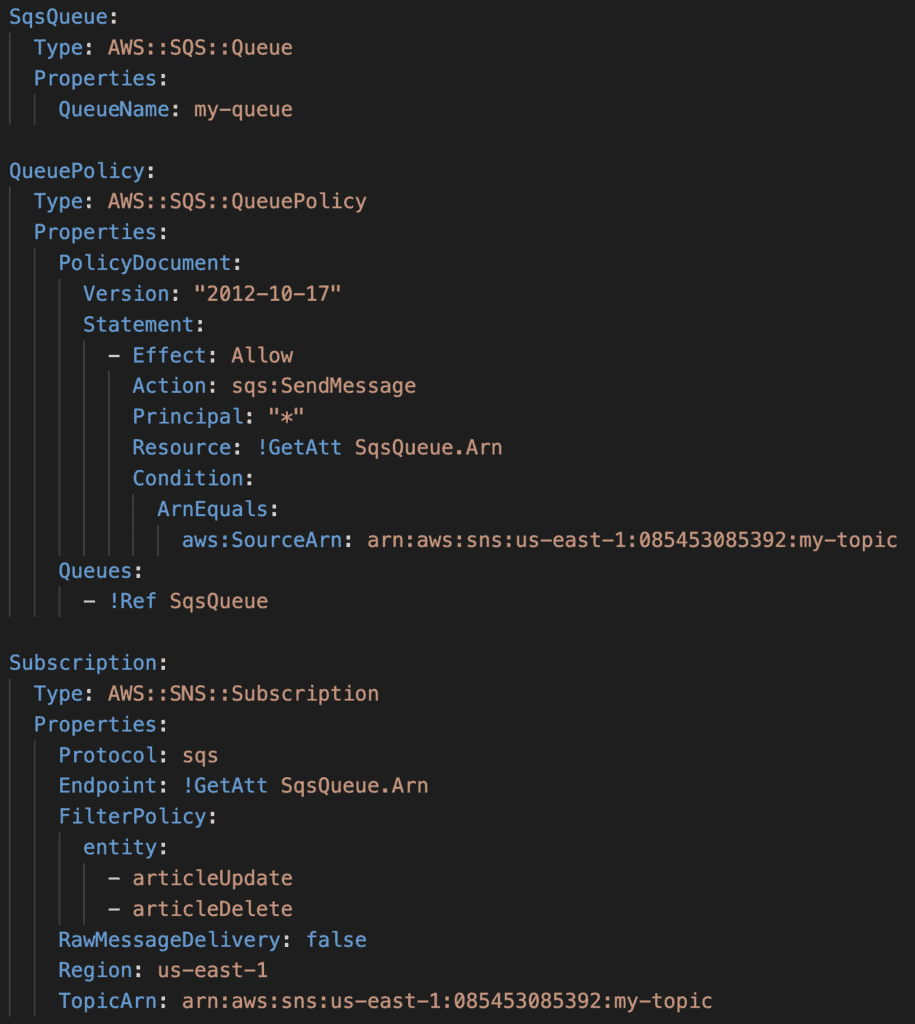
Then, in the SQS account, you need to create:
- A SQS QueuePolicy to allow the above SNS topic to call sqs:SendMessage against the relevant SQS queue(s).
- Create the SNS Subscription in the SQS account. When you create the subscription in the SQS account, you don’t need to explicitly confirm the subscription. If you create the SNS subscription in the SNS account, then a confirm subscription message is sent to the SQS queue first, which you would need to handle to confirm the subscription.
All in all, it was pretty straightforward once I figured out the magic incantation to make it work.
Anyhow, I hope you find this useful!
Whenever you’re ready, here are 3 ways I can help you:
- Production-Ready Serverless: Join 20+ AWS Heroes & Community Builders and 1000+ other students in levelling up your serverless game. This is your one-stop shop for quickly levelling up your serverless skills.
- I help clients launch product ideas, improve their development processes and upskill their teams. If you’d like to work together, then let’s get in touch.
- Join my community on Discord, ask questions, and join the discussion on all things AWS and Serverless.

