Yan Cui
I help clients go faster for less using serverless technologies.
Hi, welcome to another weekly update!
Let’s work together in 2020
Are you still on the fence about serverless and need strategic guidance on how best to safely introduce serverless to your organization and reap its benefits?
Are your engineers lacking experiences with AWS and serverless and you need help upskilling the teams?
Or maybe you’re already building things using Lambda, but you need guidance on best practices and to help you avoid costly mistakes?
Or perhaps you just want an extra pair of eyes to review what you have implemented?
I have a lot of experience and expertise with AWS and serverless and I believe I can bring a lot of value to your organization. I know we’re only in Q4 2019, but I have started accepting consulting and speaking requests for 2020. If you’re interested in working with me, you can get in touch here.
I provide a range of services, from running in-house workshops, consulting to actually working with your teams to deliver features and enhancements. I spend most of my time in the UK and the Netherlands, but I have worked with clients from all around the world including the US and Australia. I’m not particular to any industry and take my pride in my ability to adapt to the demands of my clients regardless of organization size and domain. To date, I have helped clients in both public and private sectors, in industries ranging from gaming, finance and healthcare. Some of my clients are stealth mode startups, and others are multi-national enterprises.
New posts
Should you pack the AWS SDK in your deployment artefact? A lot of folks would tell you that you shouldn’t pack the AWS SDK in your Lambda deployment artefacts but I’m here to tell you otherwise!
All you need to know about caching for serverless applications. In this post, I discussed why caching is still relevant for serverless, and where should you implement caching – the client, the CDN, in API Gateway or the Lambda function, as well as the database itself.
The API Gateway security flaw you need to pay attention to. The issue is the default rate limit for an API, and how it interplays with the regional limits. Essentially it leaves you open to attackers taking down all your APIs in a region by attacking just one endpoint.
Introducing the lumigo-cli. This is the announcement post for the lumigo-cli, which includes a bunch of helpful commands for people using Lambda.
Monitor Lambda cold start durations with CloudWatch. The 1st step to improve cold-start performance is to monitor them. Lambda is now publishing cold-start latency in REPORT logs, and we’ve got the tool to help you turn them into custom CloudWatch metrics so you can monitor them easily.
Public speaking
I gave a talk on serverless security at the sphere.it conference in Krakow this week, and the kick-off event for the ServerlessDays meetup in Amsterdam. The slides are available here:
Next week, I’m doing another run of my live online training session with O’Reilly. It’s not too late to register, you can even get it for free if you take advantage of their free trial period ;-)
On the 23rd of October, I’ll be back in London to speak at the Serverless in JustGiving event. I’ll be talking about the challenges people face when moving to serverless and common mistakes you should avoid.
Open source updates
lumigo-cli
I have been working hard on the lumigo-cli and have some wonderful updates for you :-)
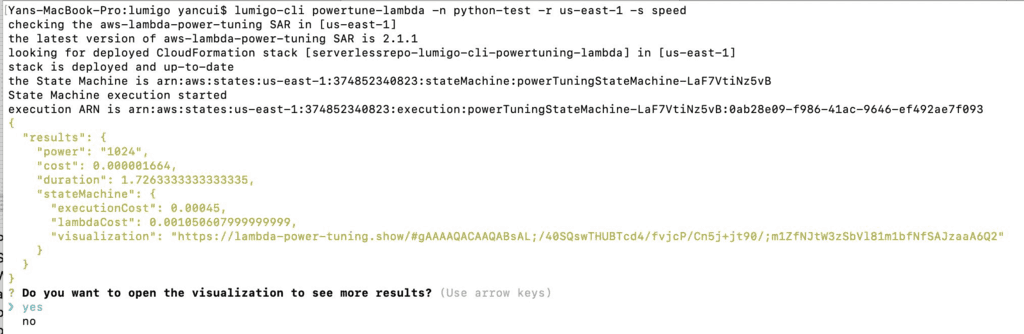
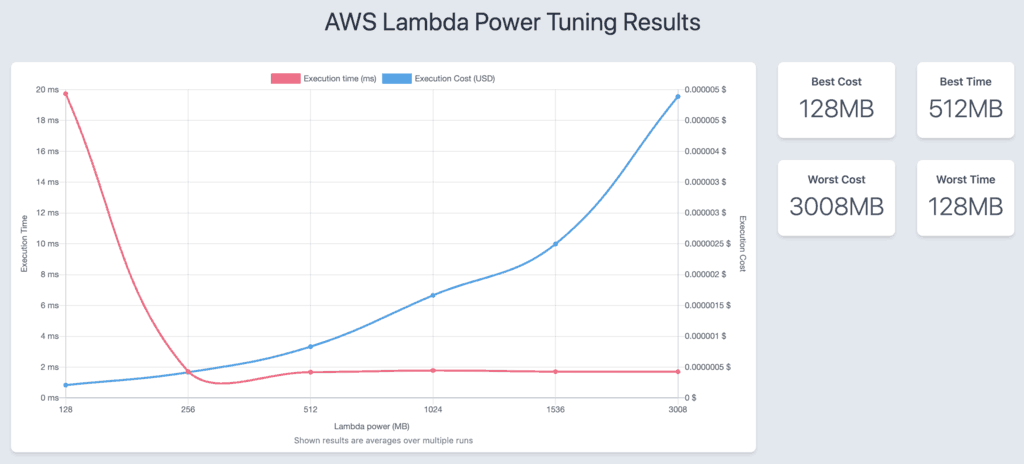
The headline news is the new powertune-lambda command. It helps you find the optimal memory setting for either speed or cost. And thanks to Alex Casalboni‘s update to the aws-lambda-power-tuning SAR, you can also visualize the result for different memory settings as well.
But that’s not all, I also added a bunch of other useful features too:
- switch-profile command to let you easily switch between different named AWS profiles.
- whoami command to see which profile you’re currently using.
- the sls-remove command lets you specify an option flag (-e) to empty all S3 buckets configured in the stack, not just the deployment bucket
- list-kinesis-shards command to list all the shards in a Kinesis stream with their usage metrics in the last hour
dazn-lambda-powertools
I’m pleased to announce two major updates for dazn-lambda-powertools:
- You can now deploy ALL the packages via a single Lambda layer.
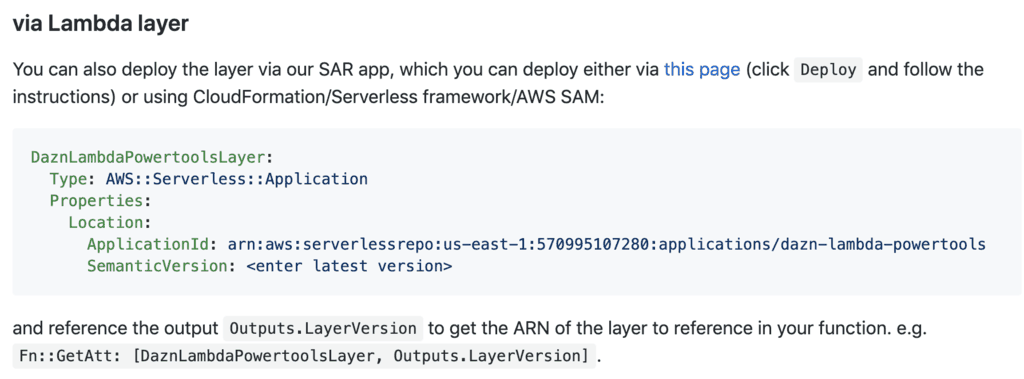
- DynamoDB Streams is supported! When you upsert a row in DynamoDB, correlation IDs are forwarded to the events in the stream, and auto-captured by any Lambda function that processes these events.
async-custom-metrics SAR
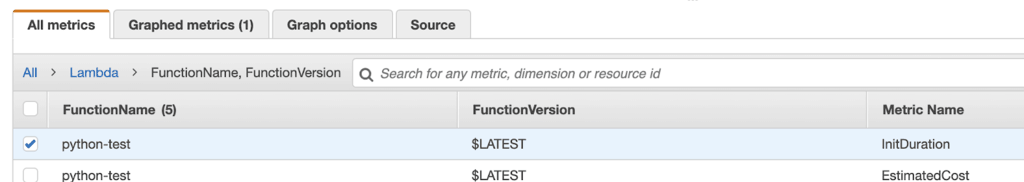
Lambda is reporting the init duration in the REPORT message at the end of a cold start.
![]()
The async-custom-metrics SAR can now parse these and turn them into custom metrics in CloudWatch.
Did you notice that when you change the tags on a CloudFormation stack, the changes are not propagated to Step Functions and IAM roles?
This has hit me a few times in the past, so I updated the propagate-cfn-tags SAR to better deal with this. Once deployed, the SAR will automatically propagate updates to CloudFormation tags to Step Functions and IAM roles for you.
Whenever you’re ready, here are 3 ways I can help you:
- Production-Ready Serverless: Join 20+ AWS Heroes & Community Builders and 1000+ other students in levelling up your serverless game. This is your one-stop shop for quickly levelling up your serverless skills.
- I help clients launch product ideas, improve their development processes and upskill their teams. If you’d like to work together, then let’s get in touch.
- Join my community on Discord, ask questions, and join the discussion on all things AWS and Serverless.