The anti-polling pattern for Step Functions
Step Functions is often used to poll long-running processes, e.g. when starting a new data migration task with Amazon Database Migration.
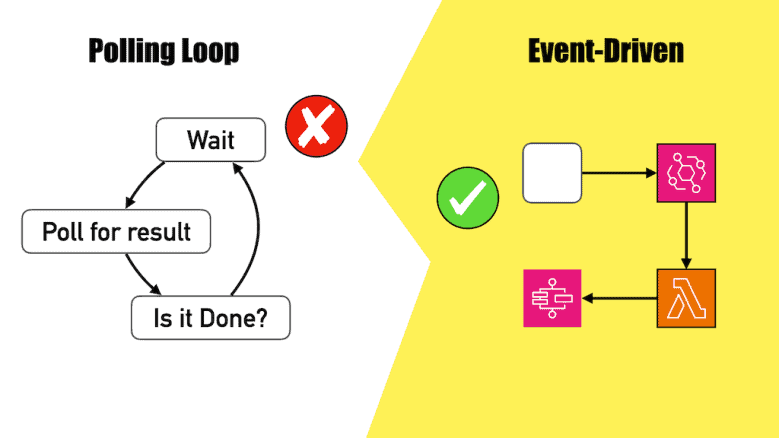
There’s usually a Wait -> Poll -> Choice loop that runs until the task is complete (or failed).
Polling is often the default solution because it’s easy, not because it’s good.
If you can get an event (or a callback), you can stop spinning your state machine and start treating “waiting” as a first-class step. Less noise, fewer transitions, lower cost.